WireGuard is a modern VPN (Virtual Private Network) technology that utilizes state-of-the-art cryptography. Compared to other popular VPN solutions, such as IPsec and OpenVPN , WireGuard is faster, easier to configure, and has a smaller footprint.
The main advantage of WireGuard is that it runs much lighter and is designed to offer encryption with less overhead. When compared to the more common OpenVPN and IPsec protocols, WireGuard demonstrates benefits with both faster throughput speeds, and lower ping times.
WireGuard utilizes the following:
- Curve25519 for key exchange
- ChaCha20 for symmetric encryption
- Poly1305 for message authentication codes
- SipHash for hashtable keys
- BLAKE2s for cryptographic hash function
- UDP-based only
WireGuard Install Step
Prerequisites
Ubuntu 20.04.2 LTS (GNU/Linux 5.4.0-73-generic x86_64)
Install WireGuard on Ubuntu 20.04
Step 1 – Update your system
sudo apt update
sudo apt upgradeStep 2 – Installing a WireGuard VPN server on Ubuntu 20.04 LTS
sudo apt install linux-headers-$(uname --kernel-release) # installs the right kernel headers for your version
sudo apt install wireguard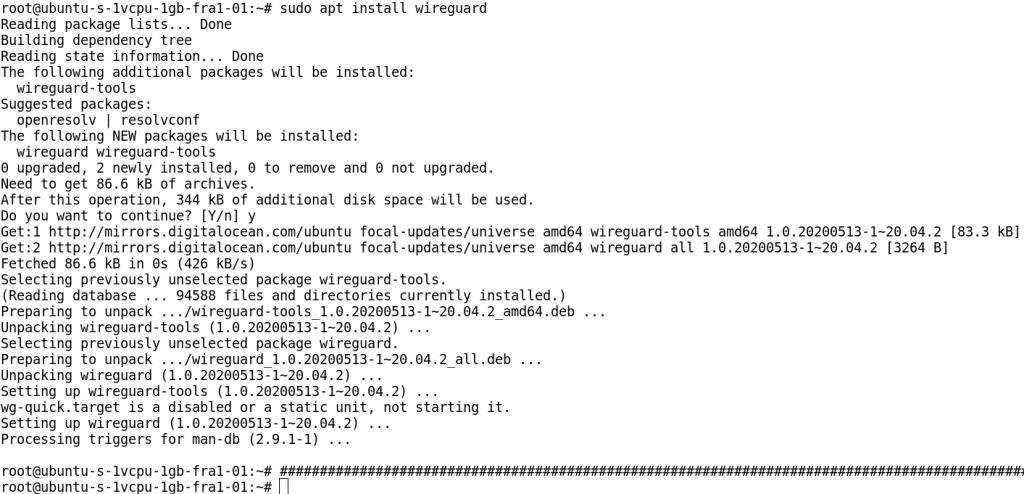
Once WireGuard is installed, you can check that the installation succeeded by running: wg, if you get no output it’s all good.
Step 3 – Configure your WireGuard Server
Run the following command to generate the key pair:
wg genkey | sudo tee /etc/wireguard/privatekey | wg pubkey | sudo tee /etc/wireguard/publickey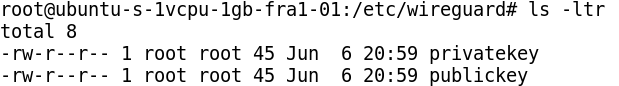
Next, copy the contents of the private key:
cat privatekeyOnce you have the contents of the private key copied to your clipboard, create a WireGuard configuration file in /etc/wireguard/wg0.conf
In the file, add the following lines and finally, save the file
[Interface]
PrivateKey = SERVER_PRIVATE_KEY
Address = SERVER_IP /mask
DNS = 1.1.1.1
ListenPort = 5555
[Peer] # we will add these lines after client wireguard install step
PublicKey = CLIENT_PUBLIC_KEY
AllowedIPs = CLIENT_IPStep 4 – Start your WireGuard service
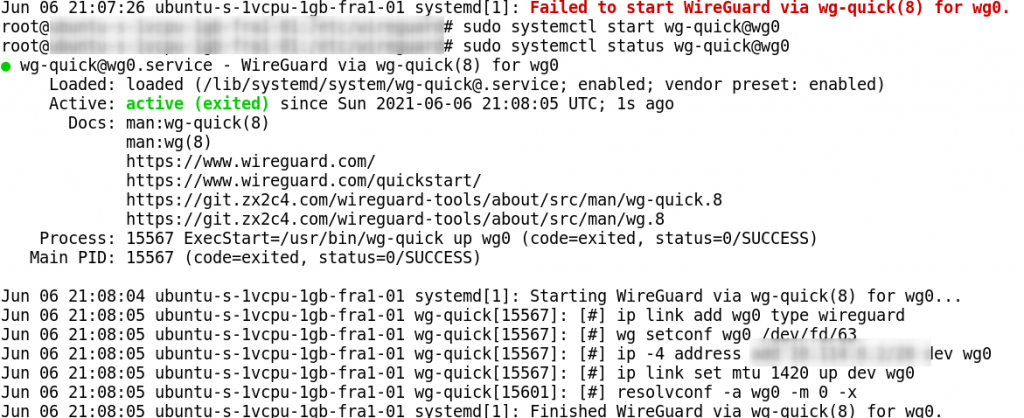
sudo systemctl enable wg-quick@wg0
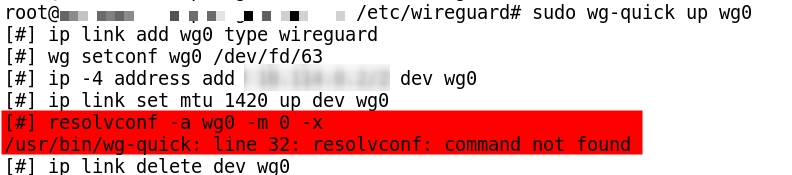
sudo wg-quick up wg0 # If you got an error for this step , you can run below command:
ln -s /usr/bin/resolvectl /usr/local/bin/resolvconf

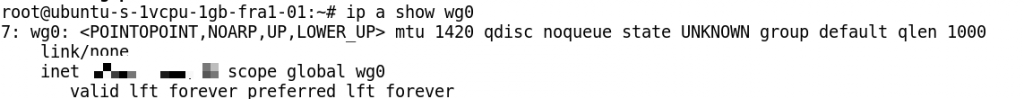
Step 5 – Check your wg command outout
wg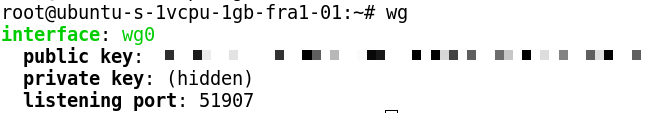
Step 6 – Configuring WireGuard Client
Next, we need to configure the WireGuard client. Ensure you have WireGuard installed on the system.
Connect your client and Generate Key value pairs as well.At this time, you should copy client public key to add to server config file.
wg genkey | sudo tee /etc/wireguard/privatekey | wg pubkey | sudo tee /etc/wireguard/publickey
vi /etc/wireguard/wg0.conf
[Interface]
PrivateKey = CLIENT_PRIVATE_KEY
Address = Client Pri IP/Mask
[Peer] # you should get this part on server
PublicKey = SERVER_PUBLIC_KEY
Endpoint = SERVER_IP_ADDRESS:5555
AllowedIPs = 0.0.0.0/0Enable and start VPN client/peer connection, run:
sudo systemctl enable wg-quick@wg0
sudo systemctl start wg-quick@wg0
sudo systemctl status wg-quick@wg0Step 7 – Verification
Check your wg command output.